What if the data your C-suite actually wants isn’t found in your firewall logs, but in your breakroom? You’ve likely felt the frustration of finishing another annual training cycle only to realize you still can’t prove your team is safer than they were in 2024. It’s a common struggle. Most security leaders agree that traditional compliance checklists feel like a guessing game when you’re trying to identify which specific departments are your highest risk. You need more than a “completed” status; you need evidence of genuine resilience.
This guide changes that. You’ll learn how to transform your next employee cybersecurity risk audit from a static document into a dynamic, behavioral assessment. We’re moving beyond passive awareness toward active Human Risk Management (HRM). By the end of this 2026 implementation guide, you’ll have a repeatable process to measure security culture, satisfy compliance, and finally provide the ROI proof your board demands. We’ll show you how to turn abstract human risk into measurable data that prioritizes your training budget where it matters most.
Key Takeaways
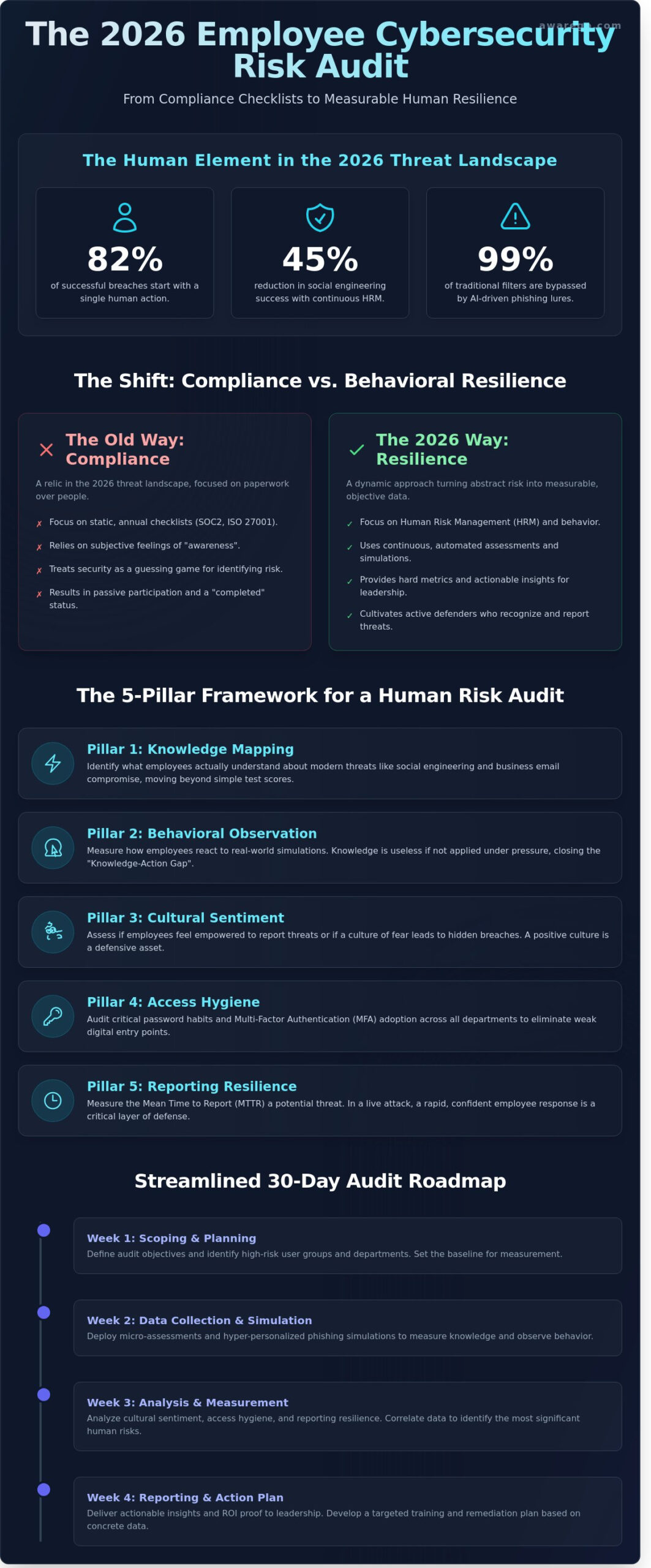
- Move beyond static annual checklists to build a resilient security culture that thrives in an AI-driven threat landscape.
- Discover a 5-pillar framework that shifts your focus from what employees know to how they actually behave during real-world simulations.
- Follow a streamlined 30-day roadmap to conduct an effective employee cybersecurity risk audit that identifies and protects your high-risk user groups.
- Learn the critical difference between checking a compliance box and fostering true behavioral resilience across your entire organization.
- See how automated Human Risk Management tools transform manual data into actionable insights that empower your team to stay safe.
What is an Employee Cybersecurity Risk Audit in 2026?
An employee cybersecurity risk audit is a systematic evaluation designed to pinpoint human-related security vulnerabilities within your organization. Historically, businesses relied on a standard Information security audit to check boxes for compliance. By 2026, this approach has become a relic. Static, annual reviews can’t keep pace with a threat environment where AI-driven attacks evolve every hour. The focus has shifted from general IT infrastructure to specialized Human Risk Management (HRM) assessments that prioritize people over hardware.
The core objective of a modern audit is to replace subjective “awareness” with objective, measurable risk data. You don’t want to guess if your employees feel safe; you need to know exactly how they’ll react when a deepfake voice clone calls their desk. Organizations using continuous HRM metrics reported a 45% reduction in successful social engineering attempts in the first half of 2026 compared to those relying on legacy methods. This shift turns “feeling secure” into a hard metric that your leadership team can use to justify security investments.
The 2026 Threat Landscape and the Human Element
AI-powered social engineering has fundamentally rewritten the rules of engagement. In 2026, 82% of successful breaches start with a single human action. Attackers now use generative AI to create hyper-personalized phishing lures that bypass 99% of traditional email filters. These “one-click” vulnerabilities are the primary focus of a modern employee cybersecurity risk audit. Remote and hybrid work models have expanded the human attack surface, making every home office a potential entry point for ransomware. You’re no longer defending a central perimeter; you’re supporting a distributed network of human decisions and digital habits.
Audit vs. Assessment: Understanding the Difference
It’s vital to distinguish between an audit and an assessment to build a resilient culture. Audits serve as point-in-time validations for compliance frameworks like SOC2 or ISO 27001. They’re necessary for your legal department and external partners. Assessments, however, function as continuous loops designed for behavioral improvement. A comprehensive strategy requires both automated tools to track real-time behavioral data and manual reviews to understand the “why” behind the numbers. This dual approach ensures your security culture is resilient, not just compliant on paper. It moves your team from passive participants to active defenders who recognize threats before they become incidents.
The 5-Pillar Framework for a Human Risk Audit
An effective employee cybersecurity risk audit moves beyond technical scans. It focuses on the people behind the keyboards. We use a five-pillar framework to turn abstract behaviors into measurable data. This approach ensures your security strategy is grounded in human reality rather than just compliance checkboxes. You can align your internal processes with the GAO Cybersecurity Program Audit Guide to ensure your methodology meets high-level standards for risk management. By treating security as a shared responsibility, you transform your workforce from a vulnerability into a defensive asset.
- Pillar 1: Knowledge Mapping. You need to identify what your employees actually understand about threats like social engineering and business email compromise.
- Pillar 2: Behavioral Observation. This measures how they react to real-world simulations. Knowledge is useless if it isn’t applied under pressure.
- Pillar 3: Cultural Sentiment. Do they feel empowered to report threats? A culture of fear leads to hidden breaches.
- Pillar 4: Access Hygiene. This involves auditing password habits and MFA adoption across all departments to eliminate weak entry points.
- Pillar 5: Reporting Resilience. We measure the Mean Time to Report (MTTR). In a live attack, every second matters.
Pillar 1 & 2: Mapping Knowledge to Action
Most organizations suffer from a “Knowledge-Action Gap.” Employees might pass a multiple-choice test but still click a suspicious link during a busy Monday morning. You should use micro-assessments to test knowledge without causing “test anxiety.” These bite-sized interactions provide a clearer picture of retention than a once-a-year seminar. In 2026, phishing simulations must mirror advanced tactics like AI-generated deepfake voices or hyper-personalized spear-phishing. If the marketing department shows a 15% higher click rate than finance, you know exactly where to focus your resources. Conducting a regular employee cybersecurity risk audit allows you to bridge these gaps with surgical precision.
Pillar 3 & 4: Culture and Access Control
Security culture isn’t about strict rules; it’s about psychological safety. Use anonymous surveys to see if employees fear punishment for reporting a mistake. If 42% of your staff hides errors to avoid trouble, your risk is invisible. You must also audit shadow IT. Unauthorized software use often stems from employees trying to be more efficient, but it creates massive blind spots. Linking your human risk assessment data directly to identity management helps you automate access levels based on real-time behavior. This makes your security seamless and effective for everyone involved, reducing friction while increasing resilience.
Compliance vs. Behavioral Resilience: A Comparison
Most organizations treat security training as a simple checklist. They ask, “Did the employee watch the three-minute video?” This approach satisfies auditors but fails to protect your network. An effective employee cybersecurity risk audit shifts the focus from passive attendance to active habit formation. While compliance measures participation, behavioral resilience measures real-world defense. Research from the Ponemon Institute indicates that organizations focusing on human-centric security can reduce the financial impact of a data breach by up to 70%.
Traditional audits often ignore the psychology behind a click. They don’t account for the stress or distractions that lead to errors. By auditing for resilience, you acknowledge these human factors. You turn your employees into a proactive sensor network rather than a passive liability. Meeting regulatory standards like GDPR or HIPAA is your baseline. It’s the floor, not the ceiling. Compliance proves you have a policy; behavioral resilience proves your people actually follow it when a phishing link hits their inbox. You aren’t just looking for “completion rates” anymore. You’re looking for a measurable shift in how your team handles sensitive data.
Meeting Regulatory Audit Requirements
A comprehensive employee cybersecurity risk audit is a critical tool for satisfying modern legal frameworks. Under ISO 27001 Annex A.7, you must demonstrate that employees understand their information security responsibilities. A behavioral audit provides the documentation needed to prove “reasonable care” under GDPR. It creates a clear audit log showing that you’ve identified specific risks and taken proactive steps to mitigate them. This aligns perfectly with the NIST Cybersecurity Framework 2.0, which emphasizes the human element as a core pillar of organizational defense.
Benchmarking Your Human Risk
You can’t improve what you don’t measure. By benchmarking human risks, you compare your organization’s performance against industry peers in sectors like finance or healthcare. This data allows you to move beyond gut feelings. You can set specific Security Culture KPIs, such as reducing the “time to report” a suspicious email or decreasing the percentage of high-risk users. Behavioral Resilience serves as the ultimate metric of a successful audit, representing the measurable ability of your workforce to consistently identify, avoid, and report digital threats through ingrained habits.
How to Conduct Your Employee Risk Audit in 30 Days
Launching your employee cybersecurity risk audit doesn’t have to be a multi-month marathon. You can gain a clear picture of your organization’s human vulnerabilities in just 30 days. By focusing on behavioral data rather than just technical logs, you transform security from a checklist into a measurable culture. This timeline ensures you gather actionable insights without slowing down your operations.
Phase 1: Preparation and Tool Selection
You don’t need months of planning. Start by assembling your core team. This includes IT for technical oversight, HR to manage the people aspect, and Legal to ensure compliance with privacy laws. Your next move is selecting a platform that supports modern human risk management software features. Look for tools that offer seamless integration and behavioral science insights. Set your baseline early. If your current phishing fail rate is unknown, aim for 100% participation to establish a true starting point.
Phase 2: Execution and Reporting
Execution happens in five streamlined steps designed to maximize clarity and minimize friction. Conducting an employee cybersecurity risk audit provides the data you need to move from reactive patching to proactive resilience.
- Step 1: Define your scope. Focus on high-risk user groups first. This includes VIPs, Finance teams, and HR staff who handle sensitive PII and large wire transfers daily.
- Step 2: Deploy automated assessments. Use non-intrusive tools to measure how employees react to real-world scenarios. This avoids “test anxiety” and provides more accurate data on actual habits.
- Step 3: Analyze “Risk Hotspots.” Look for patterns. You might find that your Sales team has excellent password hygiene but fails 22% of social engineering simulations.
- Step 4: Create a remediation plan. Don’t rely on long, boring training videos. Use micro-learning content to address specific gaps identified during the audit.
- Step 5: Present the Human Risk Report. Translate technical findings into business-risk language. Instead of discussing “malware signatures,” discuss “potential financial exposure.”
According to the 2024 Verizon Data Breach Investigations Report, 74% of breaches involve the human element. When you present your findings to the board, use concrete numbers. Show them how the average cost of a breach, which hit $4.88 million in 2024 according to IBM, can be mitigated through targeted behavioral changes. Building a continuous audit cycle prevents “risk decay” and keeps your defenses sharp as threats evolve.
Ready to see where your organization stands? Start your human risk assessment today and turn your workforce into your strongest defense.
AwareGO: Automating the Employee Risk Audit Cycle
Manual spreadsheets and annual surveys can’t keep up with modern threats. AwareGO transforms the employee cybersecurity risk audit from a seasonal chore into a continuous stream of automated insights. Our Human Risk Assessment (HRA) tool uses behavioral science to pinpoint exactly where your team stands. It measures 10 key areas of cybersecurity, including phishing, password hygiene, and remote work safety. This isn’t a stressful test for your staff; it’s a seamless part of their digital experience.
When the assessment identifies a vulnerability, the platform automatically triggers relevant micro-learning modules. These one minute videos fit into a busy workday without causing frustration. You don’t need a larger team to scale this; our system manages the cycle for 50,000 users as easily as it does for 50. This automation ensures your security posture evolves as fast as the threats do, turning potential gaps into measurable strengths.
The AwareGO Dashboard: Your Audit Command Center
The AwareGO dashboard serves as your strategic headquarters. You get an instant snapshot of your global risk profile, allowing you to compare performance across different regions or departments. It automates the complex reporting required for cybersecurity awareness training for enterprises, saving your admins roughly 10 hours of manual work per month. Our API integrations mean you can sync these insights directly with your current security stack or LMS. This creates a unified ecosystem where human risk data informs your broader security strategy. In 2024, 74% of all data breaches involved a human element; having this data at your fingertips is no longer optional.
Next Steps: From Audit to Action
An audit identifies the cracks, but action fills them. A resilient security culture relies on moving from passive awareness to active habit formation. While 80% of organizations feel they’re doing enough, data often tells a different story. A single employee cybersecurity risk audit provides the roadmap, but consistent engagement builds the shield.
Requesting a demo allows you to see your organization’s potential risk score and compare it against industry benchmarks. This isn’t about catching people out; it’s about supporting them. In 2026, your employees are your strongest defense, provided you audit them correctly and empower them with knowledge. Let’s move beyond fear and toward measurable habits together.
Build a Resilient Culture for 2026 and Beyond
Securing your organization in 2026 requires more than a simple checklist. You’ve explored how the 5-Pillar Framework and a 30-day implementation roadmap shift your strategy from passive compliance to active behavioral resilience. By focusing on measurable habits instead of just theory, you empower every person in your office to act as a confident defender. A modern employee cybersecurity risk audit identifies these critical behavioral gaps before they lead to a crisis.
AwareGO simplifies this journey by combining behavioral science with data-driven insights. Our platform is trusted by Global Fortune 500 companies and has secured multiple Cybersecurity Excellence Awards for its human-centric approach. We help you replace anxiety with actionable knowledge through seamless, snackable content that fits into any workday. You don’t have to tackle human risk alone; you can start measuring and mitigating it today.
Start Your Free Human Risk Audit with AwareGO
Your team is your strongest asset. With the right data and a supportive partner, you’ll turn digital threats into opportunities for growth and collective strength.
Frequently Asked Questions
What is the primary goal of an employee cybersecurity risk audit?
The primary goal is to identify and measure human-centric vulnerabilities within your organization’s security culture. It moves beyond technical scans to see how real people handle data and digital threats in their daily routines. By quantifying these risks, you can transform passive awareness into active resilience. This process helps you build a stronger Human Risk Management (HRM) strategy that protects both your people and your brand’s reputation.
How often should an organization conduct a human risk audit?
You should conduct a comprehensive human risk audit at least twice a year to maintain an accurate security posture. Cybersecurity threats evolve rapidly, and the 2023 Verizon DBIR showed that 74% of all breaches include a human element. Frequent assessments ensure your training stays relevant to the latest tactics used by attackers. Regular check-ins allow you to spot shifting behavioral patterns and address new habits before they become permanent vulnerabilities.
Can an employee risk audit help with insurance premiums?
Yes, completing a thorough employee cybersecurity risk audit can often lead to a 10% to 15% reduction in cyber insurance premiums. Many providers now require proof of active Human Risk Management before they’ll issue or renew a policy. By showing documented evidence of your security culture and risk mitigation efforts, you demonstrate to insurers that your organization is a lower-risk client. This proactive approach saves money and improves your overall coverage.
Is a phishing simulation considered a full risk audit?
No, a phishing simulation is just one small component of a complete human risk assessment. While simulations test specific reactions to suspicious emails, a full audit examines broader behaviors like password hygiene, physical security, and sensitive data handling. A 2022 industry study found that multi-vector assessments provide a 40% more accurate picture of organizational risk than single-topic tests. You need a holistic view to build true resilience across all departments.
How do you handle privacy concerns during an employee audit?
You handle privacy by focusing on behavioral trends and anonymized data rather than individual surveillance. We use a human-centric approach that respects GDPR and CCPA standards, ensuring 100% of personal identifiers remain protected during the analysis. The goal is to improve the collective security culture, not to punish individuals for mistakes. By being transparent about how you use the data, you build trust and encourage employees to become active partners in your security journey.
What are the most common “red flags” found in an employee risk audit?
The most frequent red flags discovered during an employee cybersecurity risk audit include reused passwords across 60% of accounts and a lack of reporting for suspicious activities. Audits often reveal that 1 in 3 employees might click a malicious link if it appears to come from an internal executive. These findings highlight specific gaps in your security culture. Identifying these habits allows you to deploy targeted micro-learning that addresses weaknesses without overwhelming your team.
How long does a typical employee risk audit take to complete?
A standard audit typically takes between 2 to 4 weeks to gather enough data for a meaningful analysis. This timeframe allows you to capture a representative sample of daily habits and digital interactions across different time zones and departments. Our seamless process integrates into your existing workflow, requiring only about 5 to 10 minutes of active participation from each employee. This efficient rhythm ensures you get actionable insights without disrupting your organization’s productivity.






