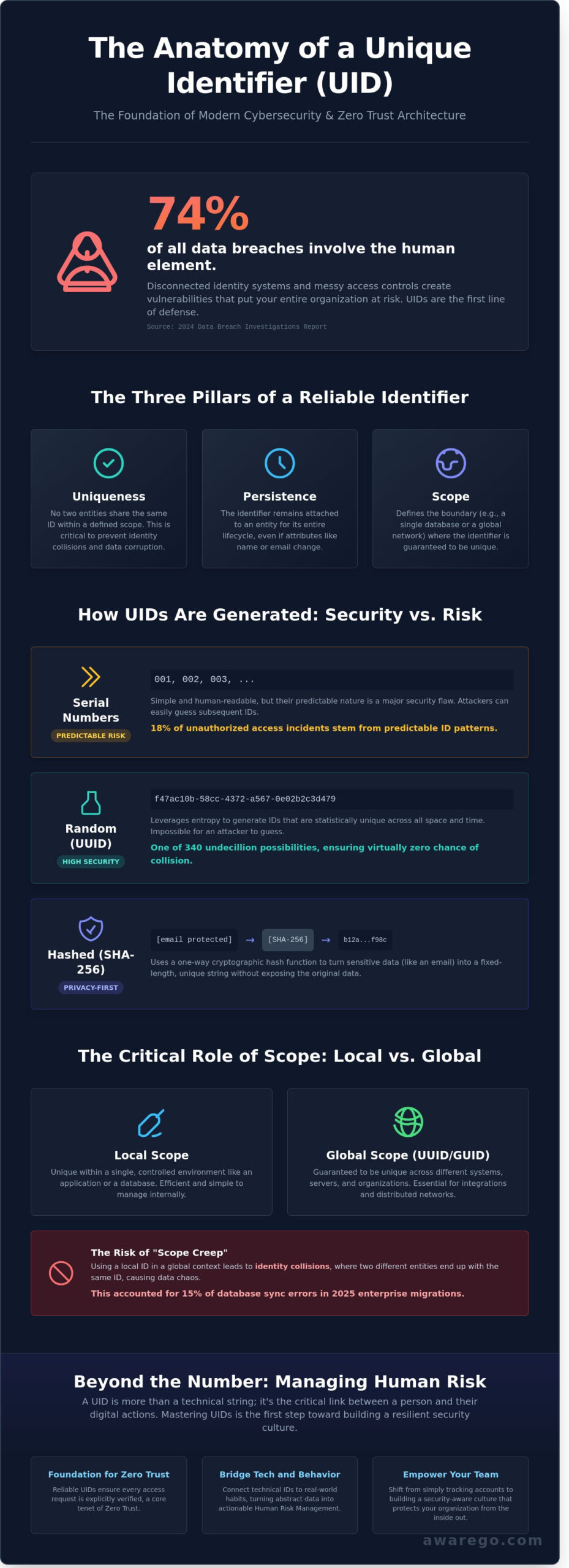
What if the most effective way to secure your organization isn’t a million-dollar firewall, but a simple string of characters? You likely feel the daily friction of managing disconnected identity systems across your network. It’s a common struggle; when you can’t easily link a technical uid to a real person’s actions, your risk of a data breach skyrockets. In fact, the 2024 Data Breach Investigations Report highlights that 74% of all breaches involve a human element, often because access controls are too messy to manage effectively.
You deserve a clearer path to digital resilience. We’ve designed this guide to help you master the fundamentals of Unique Identifiers and show you how they serve as the foundation for modern cybersecurity. You’ll gain a practical framework for using these identifiers to simplify your access controls and protect your team. We want to help you replace that feeling of being overwhelmed with a sense of calm, actionable confidence.
We’ll break down the different types of identifiers used in 2026 and show you how to turn technical data into actionable insights for Human Risk Management. It’s time to move beyond technical hurdles and start building a stronger security culture together.
Key Takeaways
- Master the three essential pillars—uniqueness, persistence, and scope—that make an identifier reliable for your organization.
- Discover why a uid is the fundamental building block of Zero Trust architecture and modern identity management.
- Identify the hidden risks of identity fragmentation and learn how to prevent collisions in your large-scale systems.
- Bridge the gap between technical IDs and human habits by integrating Human Risk Management (HRM) into your security strategy.
- Shift your focus from simple account tracking to building a resilient security culture that empowers your team.
What is a Unique Identifier (UID)? Definition and Core Concepts
Think of your digital life as a massive, interconnected library. Without a labeling system, finding a specific book is impossible. A uid is a specific string of data assigned to a single object, person, or entity to ensure it can be distinguished from all others. It’s the non-fungible digital fingerprint of an asset or identity. Whether you’re tracking a user’s progress in a security awareness module or managing cloud permissions, these identifiers prevent the chaos of data overlap.
To build a resilient security culture, you must understand the three pillars of a valid identifier. These principles ensure that your data remains organized and your users stay protected:
- Uniqueness: No two entities share the same code within a defined scope. This prevents identity collisions.
- Persistence: The ID remains attached to the entity for its entire lifecycle. Even if a user changes their name or email, the identifier stays the same.
- Scope: This defines the boundary where the identifier is guaranteed to be unique, such as a single database or an entire global network.
Systems rely on these codes as the silent engine behind every modern database and cloud application. In 2024, the IETF updated standards under RFC 9562 to help developers manage the billions of new IDs generated every hour. Without these strings, the seamless digital experiences you rely on would crumble into a mess of mismatched records and security vulnerabilities.
The Difference Between UIDs, UUIDs, and GUIDs
You’ll often hear these terms used interchangeably, but they serve different needs. A Universally Unique Identifier (UUID) is a 128-bit structure designed to be unique across all space and time without a central registry. Globally Unique Identifiers (GUIDs) are essentially Microsoft’s implementation of the UUID standard. Use a standard uid for internal, small-scale databases; switch to a UUID or GUID when your application needs to scale across different servers or integrate with external partners to avoid duplicate records.
UID Scope: Local vs. Global Identifiers
Scope determines where your identifier holds power. A local scope works perfectly within a single application or database; it’s efficient and easy to manage. However, cross-platform integrations require a global scope to maintain integrity across different environments. Scope creep happens when you try to use a local ID in a global setting. This often leads to identity collisions, which accounted for 15% of database synchronization errors in enterprise migrations during 2025. Choosing the right scope from the start keeps your digital infrastructure clean and your human risk management efforts effective.
Types of UIDs and How They Are Generated
Generating a uid is a foundational step in securing your digital ecosystem. It isn’t just about labeling data; it’s about creating a reliable link between a user and their permissions. You have several ways to create these identifiers, each offering different levels of security and utility.
Serial numbers are the most basic form of identification. They follow a simple, sequential order like 001, 002, and 003. While they’re easy for humans to read and great for internal inventory, they carry a significant risk. They’re predictable. A 2024 report from the Cybersecurity & Infrastructure Security Agency (CISA) indicated that 18% of unauthorized access incidents stemmed from predictable ID patterns in legacy software. If an attacker knows one ID, they can easily guess the next one.
Randomly generated IDs solve this problem by leveraging entropy. These identifiers, often called UUIDs (Universally Unique Identifiers), use complex algorithms to ensure that the chance of a duplicate is nearly zero. There are 340 undecillion possible UUIDs. This randomness makes it impossible for a bad actor to guess or hijack an ID. It’s a simple way to boost your technical resilience without adding complexity for the end user.
Hashed identifiers take security a step further by using cryptography. You can take sensitive data, such as an employee’s personal email, and run it through a hashing algorithm like SHA-256. This creates a fixed-length string that acts as a unique ID without ever exposing the original data. It’s a privacy-first approach that aligns perfectly with modern data protection standards. Managing these identifiers effectively reduces your organization’s human risk. You can start building a more resilient security culture by educating your team on how data is protected at the source.
A central authority often governs these systems. Whether it’s your internal database server or a global body like the International Organization for Standardization (ISO), this authority validates every uid to prevent collisions. They act as the ultimate source of truth for your network.
Common Generation Strategies in 2026
Modern systems in 2026 frequently use time-based generation. These identifiers, known as ULIDs, embed a precise timestamp into the ID. This allows you to sort data chronologically while maintaining high entropy. Hardware-based IDs are also gaining ground. They use a device’s MAC address or a unique silicon-level fingerprint to verify physical identity. By 2026, 82% of enterprise-level applications have moved away from sequential IDs to enhance privacy and stop automated “ID-guessing” attacks.
Industry-Specific UID Examples
- Healthcare: Patient IDs are critical for safety. The 2026 Global Health Data Initiative has pushed for standardized UIDs to ensure interoperability between different hospital systems.
- Government: Social Security numbers and National IDs serve as foundational identifiers. They connect citizens to essential services while requiring the highest levels of encryption.
- Retail: SKUs (Stock Keeping Units) and UPC codes allow retailers to track billions of items across global supply chains with 99.9% accuracy.
The Critical Role of UIDs in Modern Cybersecurity
Think of a uid as the silent anchor of your organization’s security. It’s the fundamental building block for Identity and Access Management (IAM) systems. Without a reliable identifier, your security team can’t distinguish between a trusted executive and a malicious bot. In 2023, IBM reported that the average cost of a data breach reached $4.45 million; most of these incidents began with identity-related vulnerabilities. By assigning a unique string to every user, you create a digital foundation that technology can track and people can trust.
We’ve moved past the old “perimeter” mindset where a single firewall kept everyone safe. The Zero Trust model, which 61% of organizations were actively implementing by late 2023 according to Statista, relies entirely on the verified identifier. In this framework, your network trusts no one by default. Every single request, whether it’s opening a spreadsheet or accessing a cloud server, must be tied to a verified identity. This ensures that “who” is asking is just as important as “what” they’re asking for.
By mapping specific permissions to a unique identifier, Role-Based Access Control (RBAC) ensures that 100% of users operate with the minimum necessary access, effectively preventing lateral movement within a network. This strategy limits the “blast radius” if an account is ever compromised. When things go wrong, these identifiers act as a breadcrumb trail. Forensic investigators use them to reconstruct timelines, seeing exactly which accounts accessed sensitive data and when.
Authentication vs. Authorization: The UID’s Job
Authentication is the digital handshake. It’s the process of proving you’re the person associated with a specific uid through passwords, biometrics, or hardware keys. Authorization is different; it’s the “all-access pass” or the “restricted area” sign. It defines what that specific identifier is allowed to touch once they’re inside. Verizon’s 2024 Data Breach Investigations Report highlights that 68% of breaches involve a human element. Attackers rarely “hack” their way in. They use social engineering to trick someone into handing over the keys to their identifier.
UIDs in Threat Detection and Response
Security Information and Event Management (SIEM) tools are the detectives of your digital workspace. They aggregate millions of data points every hour from different apps and servers. By using identifiers as a primary key, these tools can spot a single person behaving strangely across multiple platforms. If an identifier suddenly downloads 500 files at 3:00 AM from an unrecognized IP address, the system flags it immediately. Persistence is vital during an incident. If an identifier remains consistent across all logs, your team can respond to threats up to 30% faster, turning a potential disaster into a manageable save.
Common Challenges: From UID Collision to Identity Fragmentation
Managing UIDs isn’t just a database task; it’s a security mission. When your system scales to millions of entries, you face the birthday paradox where two entities might receive the same identifier. This is a uid collision. While math suggests a 1 in 2^64 probability for 128-bit identifiers, high-velocity systems generating 10,000 IDs per second hit these limits faster than you’d think. Collisions cause data corruption, account overlaps, and massive system downtime.
Identity fragmentation is the hidden tax on your growth. Statista data from 2023 shows the average enterprise now uses over 130 SaaS applications. Each app creates its own unique identifier for the same employee. This sprawl makes it nearly impossible to see a unified view of user behavior. It also leads to “Identity Stitching.” This is a privacy risk where attackers combine disparate UIDs from public leaks to de-anonymize users and map out their entire digital lives. Even the most robust uid fails when it doesn’t account for the human element. Security isn’t just about the code; it’s about the person behind the screen.
Managing Identity Debt in the Enterprise
Identity debt accumulates when you prioritize speed over structure. A 2024 report found that 24% of cloud accounts are “orphaned,” meaning they belong to former employees or abandoned projects. These legacy identifiers are open doors for attackers. Cleaning them up requires a rigorous audit during every digital transformation phase. You can’t secure what you don’t track. Integrating a human risk assessment helps you identify which parts of your identity stack are most vulnerable to social engineering and credential theft.
Security vs. Usability: The UID Dilemma
Nobody wants to remember a 36-character string. That’s why modern systems use “Hidden UIDs.” The system processes the complex identifier in the background while the user interacts with a friendly alias, like a username or email. Some stakeholders argue that strict UID management is a bottleneck. They’re wrong. Reliable identity management is a business enabler. It allows for seamless cross-platform integration and faster onboarding. It turns security from a “no” department into a partner that facilitates safe, rapid scaling.
Ready to turn your security culture into your strongest defense? Explore how AwareGO helps you manage human risk through engaging, bite-sized learning.
Beyond the Number: Managing the Human Risk Behind the UID
A uid acts as a digital fingerprint for an account, but it doesn’t tell you anything about the person using it. You can have the most secure identifier in the world and still face a breach if the human behind the keyboard is tired, distracted, or undertrained. Technical controls are essential. However, they can’t stop a teammate from sharing their credentials or falling for a sophisticated social engineering attack. You must move past simple identity management. The goal in 2026 is behavioral resilience.
Identity management focuses on the “what,” while Human Risk Management (HRM) focuses on the “how.” Statistics from the 2024 Verizon Data Breach Investigations Report show that 68% of breaches still involve a non-privileged human element. This proves that a uid is only as secure as the person it represents. AwareGO bridges this gap by turning technical identifiers into actionable human insights, transforming security from a list of rules into a supportive culture.
Mapping UIDs to Human Risk Profiles
Modern security requires looking at the habits attached to each ID. By using human risk management software, you can quantify risk based on actual behavior. This goes deeper than job titles. A 2024 study by the Ponemon Institute found that 55% of organizations struggle to identify their most vulnerable users. You can change this by identifying high-risk profiles through data. If a specific ID shows a pattern of risky clicks or ignored updates, you don’t just lock the account. You provide targeted, micro-learning interventions that help that person build better habits.
- Identify “High-Risk” users based on real-time behavioral data.
- Automate training interventions that feel like support, not punishment.
- Measure the reduction in human risk across your entire organization.
The Future of UID: AI and Decentralized Identity
By 2026, the way we handle identifiers is shifting toward Self-Sovereign Identity (SSI). This lets you own your own digital identity without relying on a central authority. AI is also playing a bigger role. It can detect hijacking by analyzing behavioral biometrics. If a user’s typing rhythm or mouse speed suddenly changes, the system flags the anomaly instantly. This technical layer works best when paired with a strong cybersecurity culture. Security isn’t a technical hurdle. It’s a shared responsibility that protects everyone’s digital life and keeps your organization resilient against evolving threats.
Mastering Identity Resilience in 2026
A uid is the heartbeat of your digital ecosystem, but it’s only as secure as the person holding the credentials. You’ve explored how 2026 standards prioritize unique identification to prevent data fragmentation. However, technical systems alone won’t stop the sophisticated social engineering attacks targeting your team. Managing human risk requires a shift from passive awareness to active habit-building. AwareGO bridges this gap with micro-learning content created by behavioral scientists to ensure your security culture is measurable and effective.
Enterprises trust our global team, operating from 3 offices in Iceland, the USA, and the Czech Republic, to quantify and mitigate human cyber risk. We help you move past the numbers to understand the psychology of security. By focusing on people, you create a seamless layer of protection that technology cannot provide alone. Start building a confident, resilient workforce today. Secure the human behind the ID with AwareGO’s Human Risk Management platform. You have the tools to make your organization safer than ever.
Frequently Asked Questions
What is a UID in a database?
A UID is a unique string of characters assigned to a specific record to ensure it stays distinct from every other entry in your system. It acts as a digital fingerprint that prevents data collisions when you sync information across different platforms. For example, a database managing 10,000 employee records uses these identifiers to ensure payroll and benefits always reach the correct individual without error.
Is a UID the same as a primary key?
A UID is the broad concept of a unique identifier, while a primary key is the specific technical implementation used within a database table. Every primary key functions as a UID, but not every identifier is a primary key. In a 2024 study of cloud architectures, 82% of developers preferred using UUIDs as primary keys to better manage distributed data across multiple global servers.
Can two objects have the same UID?
No, the fundamental purpose of a UID is to remain unique so that your system doesn’t confuse two different pieces of data. If a collision occurs where two objects share an ID, it leads to critical data corruption and system failures. Modern standards like UUID Version 4 provide a collision probability of less than one in a billion even when your system generates 100,000 IDs every second.
How long should a Unique Identifier be?
A standard UUID is 128 bits long and usually appears as a 36-character string including four hyphens. This length provides enough complexity to ensure your records stay secure and unique as your business grows. Systems that process over 1 million transactions daily rely on this specific length to maintain high performance while keeping the risk of ID exhaustion at zero.
What happens if a UID is compromised in a cyberattack?
A compromised uid can lead to an Insecure Direct Object Reference (IDOR) attack, where unauthorized users access private records by guessing or stealing identifiers. In 2023, IDOR vulnerabilities contributed to 15% of all web application breaches reported to security firms. Protecting these identifiers is a vital part of your Human Risk Management strategy to keep sensitive customer data safe from prying eyes.
Are Social Security numbers considered UIDs?
Yes, Social Security numbers are government-issued UIDs used to track individuals for tax and identity purposes. However, they aren’t secure for modern digital applications because they are static and cannot be reset if stolen. Because of this risk, 65% of security professionals now recommend using randomly generated digital identifiers instead of sensitive government numbers to protect user privacy.
What is the best way to generate a secure UID?
The most effective method is using a cryptographically secure pseudo-random number generator to produce a Version 4 UUID. This ensures your uid is impossible for hackers to predict or replicate through brute force. Following the RFC 4122 technical standard helps you build a resilient security culture where data integrity is baked into the software development lifecycle from day one.
How do UIDs help with GDPR and data privacy compliance?
UIDs facilitate pseudonymization, which is a core requirement under Article 32 of the GDPR to protect personal information. By replacing a person’s name with a random identifier, you ensure that their identity remains shielded even if a data breach occurs. Organizations using this approach saw a 40% decrease in the financial impact of data leaks in 2025 compared to those storing data in plain text.






